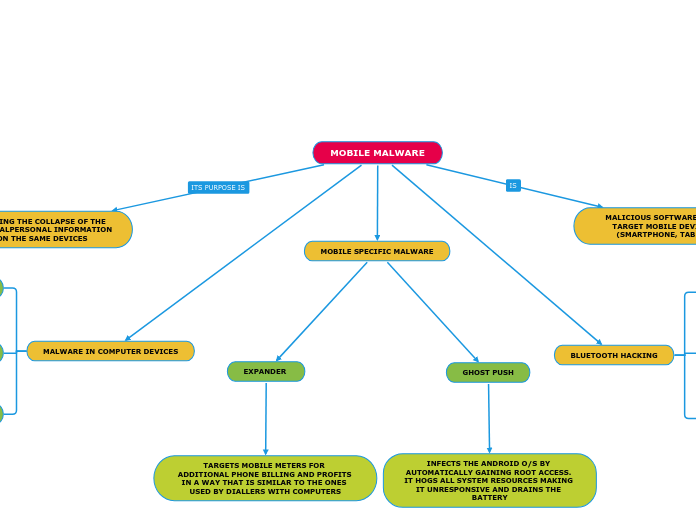
MOBILE MALWARE
MALICIOUS SOFTWARE DESIGNED TO TARGET MOBILE DEVICE SYSTEMS (SMARTPHONE, TABLET OR PDA)
BLUETOOTH HACKING
BLUESNARFING
HACKERS CAN PURCHASE SOFTWARE TO ALLOW THEM TO REQUEST INFORMATION FROM USER'S DEVICES
BLUEBUGGING
AN ATTACK TO GAIN TOTAL ACCESS AND CONTROL OF A DEVICE. THE HACKER CAN ACCESS ALL THE INFORMATION ON THE SMARTPHONE, INCLUDING PHOTOS, APPS, CONTACTS
BLUEJACKING
A HACKER SEARCHES FOR DISCOVERABLE DEVICES IN THE AREA AND THEN SENDS SPAM IN THE FORM OF TEXT MESSAGES TO THE DEVICE
MOBILE SPECIFIC MALWARE
GHOST PUSH
INFECTS THE ANDROID O/S BY AUTOMATICALLY GAINING ROOT ACCESS. IT HOGS ALL SYSTEM RESOURCES MAKING IT UNRESPONSIVE AND DRAINS THE BATTERY
EXPANDER
TARGETS MOBILE METERS FOR ADDITIONAL PHONE BILLING AND PROFITS IN A WAY THAT IS SIMILAR TO THE ONES USED BY DIALLERS WITH COMPUTERS
THAT OF CAUSING THE COLLAPSE OF THE SYSTEM OR STEALPERSONAL INFORMATION STORED ON THE SAME DEVICES
MALWARE IN COMPUTER DEVICES
SPYWARE
MONITORS THE SYSTEM AND SYNCHRONISES WITH CALENDARS, EMAIL ACCOUNTS, NOTES AND ANY OTHER SOURCE OF INFORMATION TO SEND DATA TO A MALICIOUS SERVER
WORM
MAY BE TRASMITTED VIA TEXT MESSAGES (SMS OR MMS) AND TYPICALLY DOES NOT REQUIRE THE USER'S INTERACTION FOR EXECUTION
TROJAN HORSE
INTO SEEMINGLY ATTRACTIVE AND NON-MALICIOUS EXECUTABLE FILES OR APPS THAT ARE DOWNLOADED INTO THE DEVICE AND EXECUTED BY THE USER