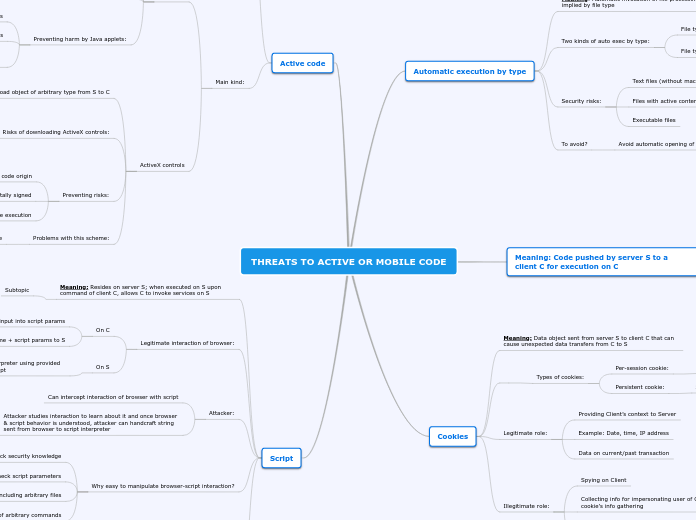
THREATS TO ACTIVE OR MOBILE CODE
Automatic execution by type
Meaning: Automatic invocation of file processing program implied by file type
Two kinds of auto exec by type:
File type implied by file extension
e.g., MS Word automatically invoked for file.doc
File type implied by embedded type
eg., File named “class28” without extension has embedded info that its type is “pdf”
Security risks:
Text files (without macros!)
Files with active content
Executable files
To avoid?
Avoid automatic opening of files by built-in handlers
Meaning: Code pushed by server S to a client C for execution on C
Example : Website with animation
Implementation 1
- S executing animation (Network bandwidth)
- Each new animation frame must be sent from S to C for display on C
Implementation 2
- S sends animation code for execution to C
- C executes animation
- Each new animation frame is available for display locally on C
Conclusion
Implementation 2 is better because saves S’s processor time and network bandwidth
Cookies
Meaning: Data object sent from server S to client C that can cause unexpected data transfers from C to S
Types of cookies:
Per-session cookie:
Stored in memory, deleted when Client’s browser closed
Persistent cookie:
Stored on disk, survive termination of Client’s browser
Legitimate role:
Providing Client’s context to Server
Example: Date, time, IP address
Data on current/past transaction
Illegitimate role:
Spying on Client
Collecting info for impersonating user of Client who is target of cookie’s info gathering
Attacker who intercepts X’s cookie can easily impersonate X in interactions with Server
Active code
Meaning: Recall: code pushed by S to C for execution on C. As demand on server S’s computing power grows, S uses client C’s computing power and
S downloads code to C (for execution on C), C executes it.
Main kind:
Java code
Designed to be truly machine-independent
Security
Strongly typed
Enforces type checking
Security flaws in JVM implementations
No type checking for some data types
Preventing harm by Java applets:
Control applets’ access to sensitive system resources
Clear memory before its reuse by new objects
Control inter-aplet communication & applets’ effects on environment
ActiveX controls
Allows to download object of arbitrary type from S to C
Risks of downloading ActiveX controls:
If handler (or viewer) for type T is available, it is invoked to present object
E.g., after file.doc downloaded, MS Word is invoked to open file.doc
If no handler for type T exists on C, C asks S for handler for T then uses it to present object
E.g., attacker defines type .bomb
Preventing risks:
Authentication scheme to verify code origin
Downloaded code is digitally signed
Digital signature verified before execution
Problems with this scheme:
It does not verify correctness of code
Script
Meaning: Resides on server S; when executed on S upon command of client C, allows C to invoke services on S
Subtopic
Legitimate interaction of browser:
On C
Browser organizes user input into script params
Browser sends string with script name + script params to S
On S
Named script is executed by script interpreter using provided params, invoking services called by script
Attacker:
Can intercept interaction of browser with script
Attacker studies interaction to learn about it and once browser & script behavior is understood, attacker can handcraft string sent from browser to script interpreter
Why easy to manipulate browser-script interaction?
Programmers often lack security knowledge
Don’t double-check script parameters
Some scripts allow including arbitrary files
Some scripts allow execution of arbitrary commands
Scripting language
CGI (Common Gateway Interface)
Enables a client web browser to request data from a program executed on the Web server
HTTP without CGI
When Web browser looks up URL, browser contacts HTTP server with this URL. HTTP server looks at filename named in URL & that file is sent back and browser displays file in the appropriate format
HTTP with CGI
When file in certain directory is named in URL (sent by browser), file is not sent back but executed as CGI script (a program). Only CGI script output is sent back for browser to display.