Authentication Mind maps - offentligt galleri
Udforsk vores store offentlige samling af authentication-mind maps skabt af Mindomo-brugere over hele verden. Her kan du finde alle offentlige diagrammer, der er relateret til authentication. Du kan se disse eksempler for at få inspiration. Nogle diagrammer giver dig også ret til at kopiere og redigere dem. Denne fleksibilitet giver dig mulighed for at bruge disse mind maps som skabeloner, hvilket sparer tid og giver dig et stærkt udgangspunkt for dit arbejde. Du kan bidrage til dette galleri med dine egne diagrammer, når du har gjort dem offentlige, og du kan være en inspirationskilde for andre brugere og blive omtalt her.


Routings
af CCNA CCNA


CISSP: Access Control Systems and Methodology
af Walkowska Anna


MicroServices
af Mike Ton

Virtual Private Netw
af sihui lau


IT Security Terms
af Usama Amin


MS302-303 Section 1: Planning Network Infrastructure
af James Herbert

wireless LAN vulnerabilities
af nursyafeera azeera


TPM (TimUR Performance Management)
af Alfiah Khoirunisa

Authentication inter-operability FreeIPA / AzMan
af ericdes (Eric)

Edgar Collins and the new Cezanne
af kinda tarek

Remote Access
af sihui lau


A Paul Cézanne painting
af ALi Abd El-Latif

Auth
af Ivan Kayzer


Authentification/De-authentifiction of Artwork
af Olivia Quinn


Classwork # 8
af Darya Fatih


5c
af soha osman
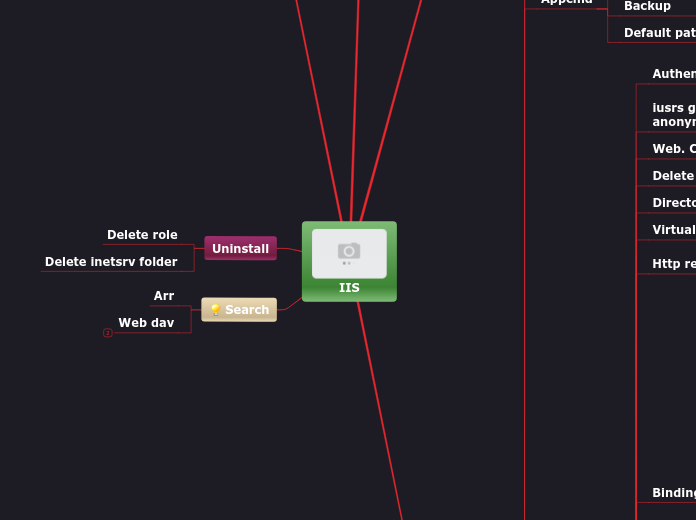

iis
af Behnam shiri

MS301 Obj 6. Implementing, Managing, and Troubleshooting Network Protocols and Services
af James Herbert

Sample Mind Map
af Octavio Hernandez


BangAli
af Yovi Oktofianus


AD Polling Mode
af Nestor Catacora

Access Contol
af Kenneth Gourlay


As Light Meets Matter: Art Under Scrutiny
af Dalia Kamar


As Light Meets Matter: Art Under Scrutinity
af Farah Anwar

Virtual Private Netw
af sihui lau

Assi 4a
af Khaled Mohsen


Mental Health
af Suresh kumar Mukhiya

YS
af Ken Reid

AD, OD and Cent Workflow
af Cheryl Lynn
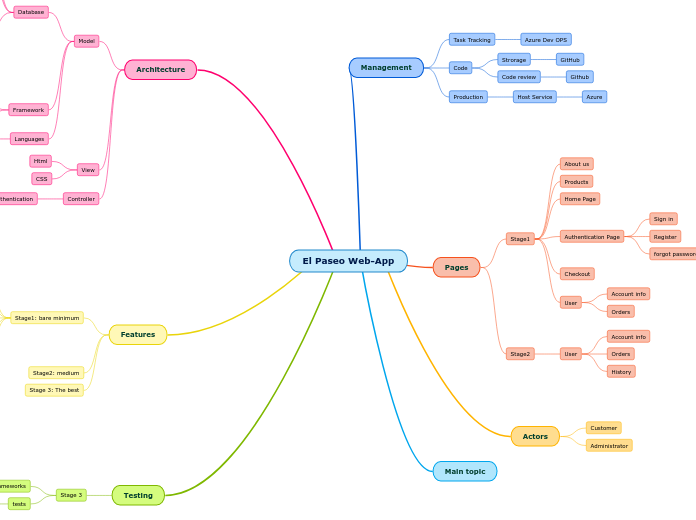

El Paseo Web-App
af Geraldine Davila


InfrastructureSecurityComponents
af Iben Rodriguez
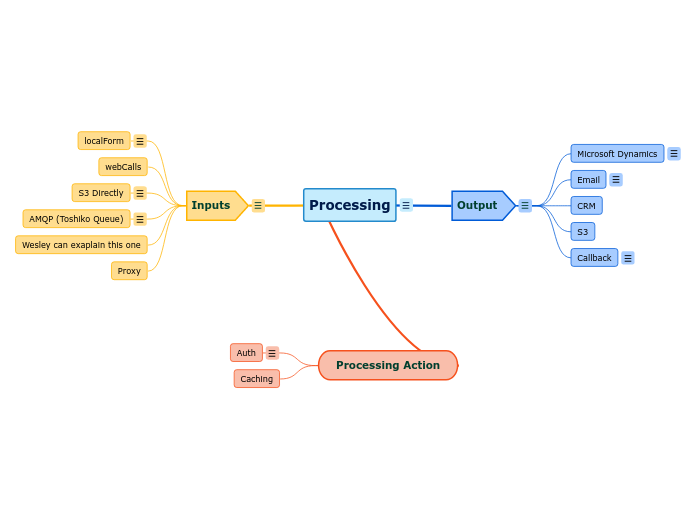

Processing
af Taibi Aymane

Authenticating Famous Works of Art
af Clarissa Pharr
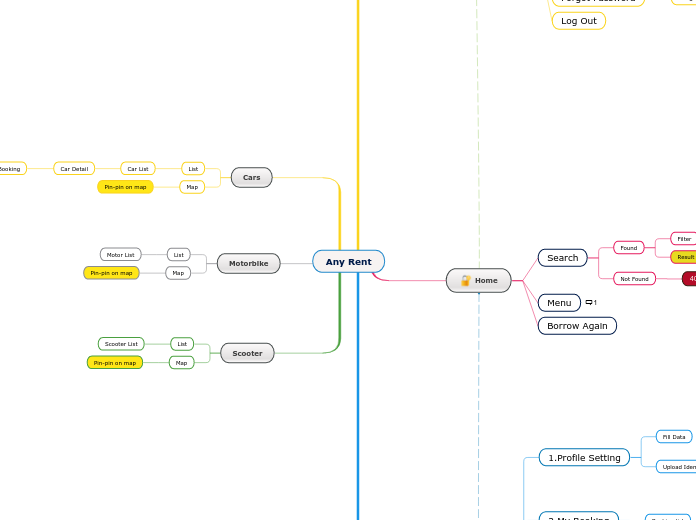

Any Rent
af Syahdan Hidayat
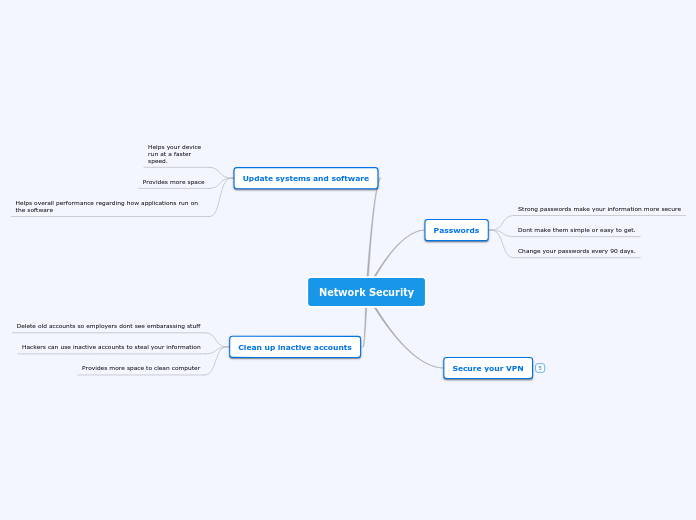

Network Security
af Jake Kilgore

Sample Mind Map
af lama hazaa

Art under scrutiny
af Noha Marei
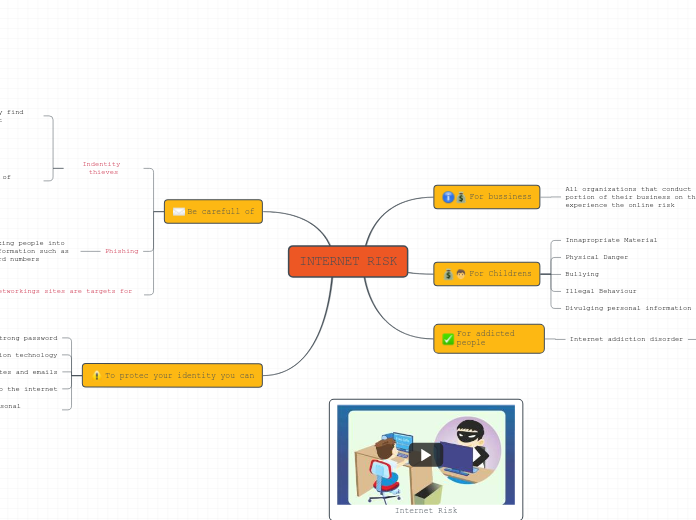

INTERNET RISK2
af Shakirs Franco
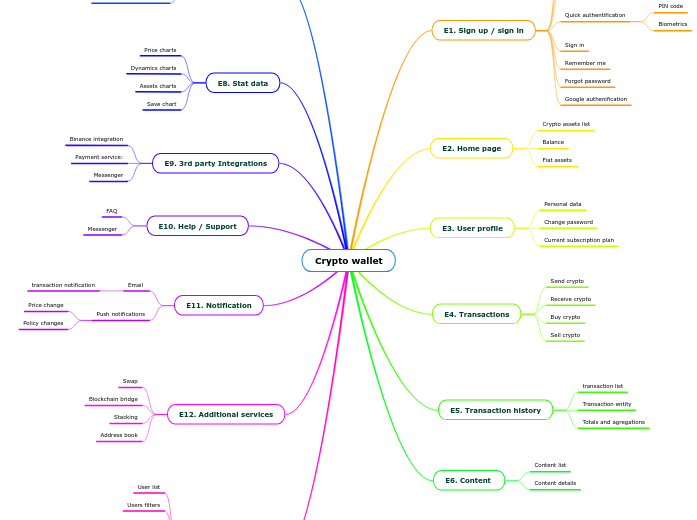

Crypto wallet
af Volodymyr Ponomarenko
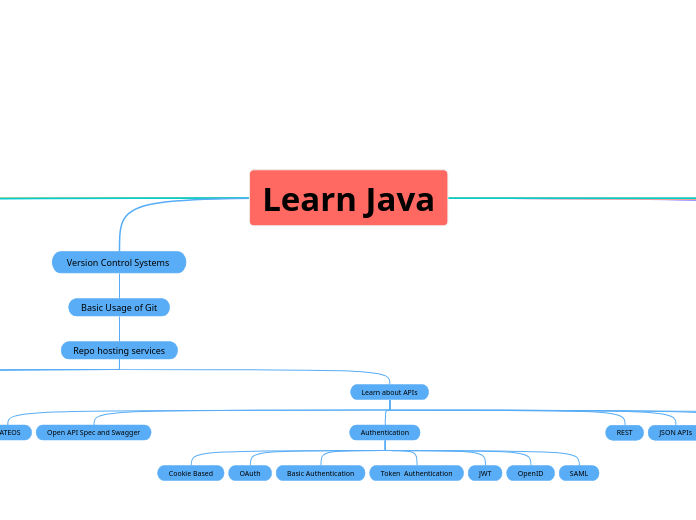

Learn Java
af Артур Базанов
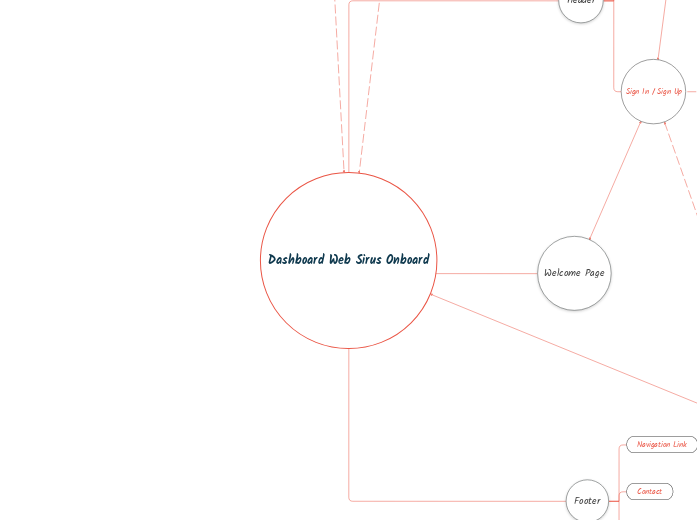

Mind Map Projek Onboard Sirus
af Aditya Wibowo
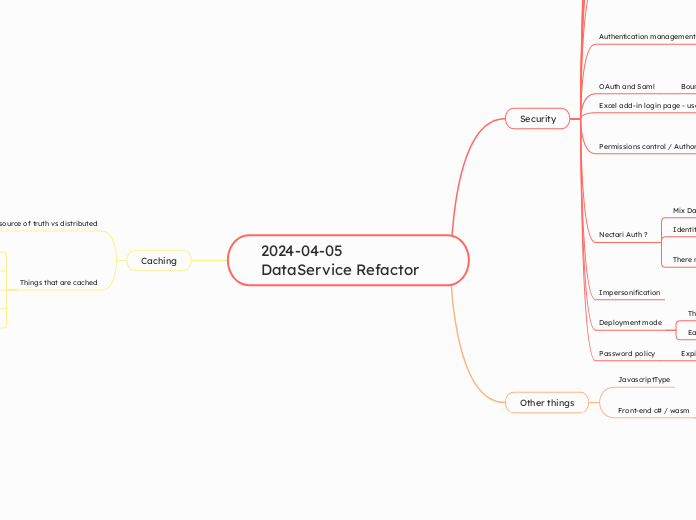

2024-04-05 DataService Refactor
af Samy Sarem
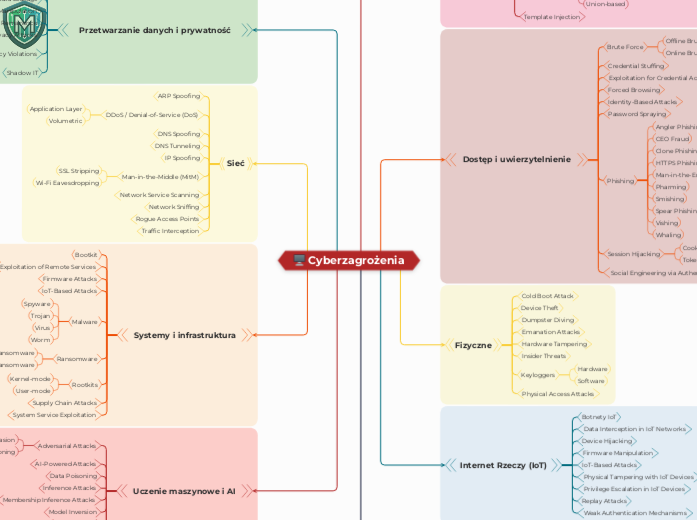

Cyberzagrożenia
af dr inż. Michał Malinowski
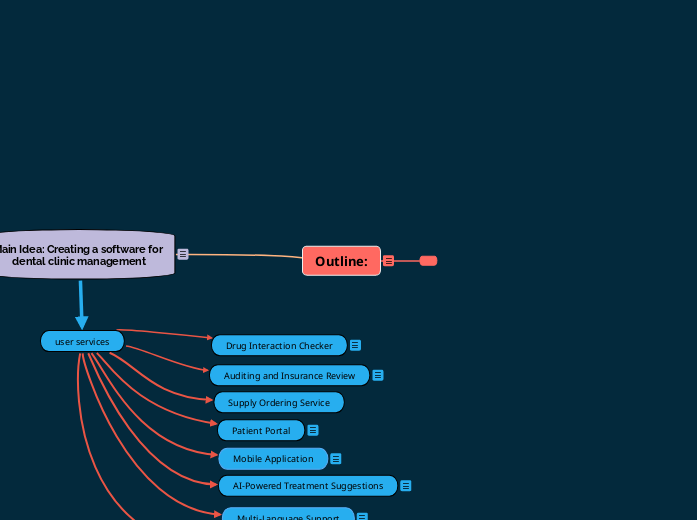

Outline: - Copy
af code clinic
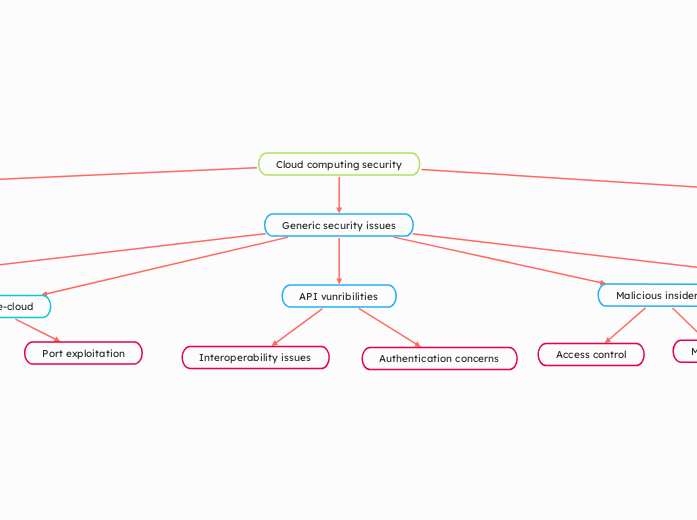

Cloud computing security
af Jack Barnes



