Inmersion in the Cloud
1.2.6 Digital Responsability
Nowadays it is very normal for someone to use social networks. What few know is that by registering with it and sharing statuses, photos, videos, among others, you let other people capture it and make it for personal use. Although we use social networks to communicate with friends or family, we also do not know who accesses them, putting important personal data that may include accounts at risk. It is our responsibility as a user to know what we post, what we use the publications of others and always respect everyone since we never know the dimension that our comments could reach.
Some damages to which we are exposed on the internet are:
Cyberaddiction. It is when you lose control over the use of the internet, thus isolating yourself from society and basing your life on the web. How can we detect cyber addiction?
Obsession for messages or social networks.
Insomnia
Isolation from friends and family.
Anxiety about not being connected to the internet.
Abuse of the time of the use of the internet and social networks.
Irritability.
Decreased academic performance.
Cyberbullying. It is when a person feels intimidated, threatened, harassed, humiliated, embarrassed or abused by another person. It arises in different ways such as insults or discrimination against a person, making public information about a person, theft and identity theft, threats of physical harm, among others. Some types of cyberbullying are:
Offensive posts on blogs, forums,
websites, and social media.
Theft of passwords.
Harassment by instant messaging.
Grooming. It is the sequence of acts that an adult does with a minor, making him his "friend" by asking for things in return, thus committing him to severe things. It's like some kind of blackmail.
1.2.5 Data Protection
1.2.5.1 Introduction
When we enter a web page, social network, etc., we begin to share information not only with the person we speak but with many more people who access the network. That is why we must have protection for our personal data.
B. What is Data Protection?
Data protection are actions that are developed so that your information is safe, that only whoever you decide has access to it.
A.What are a Personal Data?
Personal data is information related to our person that identifies us, gives us identity, describes and specifies our age, address, telephone number, personal email, academic, work or professional history, inheritance, social security number, CURP, among others. Although also more sensitive or delicate things such as our way of thinking, state of health, ethnic and racial origin, physical characteristics such as DNA or fingerprint, ideology and political opinions, religious or philosophical beliefs or convictions, sexual preferences, among others. You provide this information by authorizing the use of personal data. When writing this information on any page, be sure that their policies and reasons for you to give them to them are: What information do they require? What do they want it for? Who will have access to it? Who will be responsible for their custody?, How will they protect your data (their security measures)?
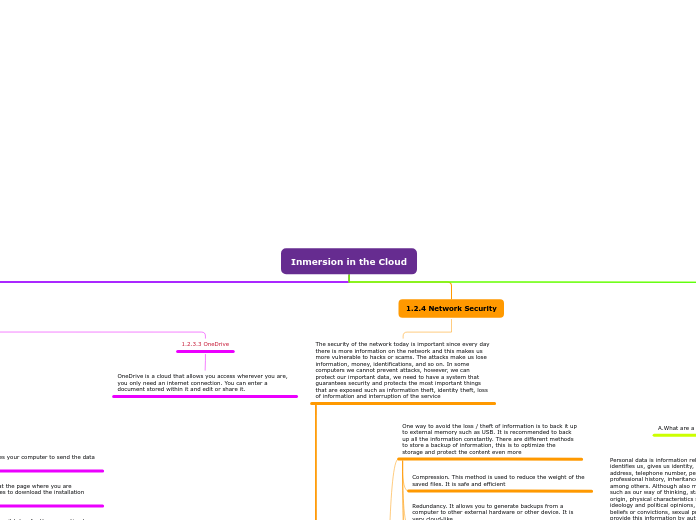
1.2.4 Network Security
The security of the network today is important since every day there is more information on the network and this makes us more vulnerable to hacks or scams. The attacks make us lose information, money, identifications, and so on. In some computers we cannot prevent attacks, however, we can protect our important data, we need to have a system that guarantees security and protects the most important things that are exposed such as information theft, identity theft, loss of information and interruption of the service
H. Access Accounts
To have more security for your data on your computer that many use it, it is recommended to create access accounts so that your personal information can only be accessed by you.
G. Firewall
Apart from having an antivirus installed, it is also essential to have a firewall that monitors the entry and exit of information traffic and restricts unauthorized access. This prevents unauthorized users from entering the computer or private network connected to the internet. These are some functions of the firewalls:
Allows inbound and outbound traffic that exists between networks and computers.
Control communication between computers and other IT equipment on the internet.
Blocks applications that may pose a risk to the computer or the network.
Establishes a barrier that prevents unauthorized access to the computer or network.
F. How do I Protect Myself from Phishing?
To avoid phishing, here are some recommendations:
The acronym for "http" is hypertext transfer protocol which is the protocol on which the internet is based. When "http" has an "s" at the end ("https") it means that this page complies with all security protocols.
Verify that the address or web page begins with the initials "https" instead of "http" as the "s" stands for secure.
Do not click on the web page within an email of questionable origin.
Avoid downloading or installing programs that come from unofficial sources, appear in pop-up windows, or appear in advertisements.
Avoid opening emails that denote spelling quality.
Avoid opening emails that are in the junk folder.
Don't open emails from unfamiliar people or companies.
Mouse over the link to verify its security.
E. What is Phishing?
'Phishing' is identity theft. It deceives people or users, shares their confidential information, such as access accounts, passwords, credit card numbers, among others. It behaves in the following way: the person receives a message in their email inbox that imitates a company or person, when the person opens said email or message, they are asked to immediately access a site or web page . In case the person or user clicks on the link, they are presented with a copycat page of the real one. At that moment the same page requests your confidential information and in this way your data is stolen.
D. What is Spam?
Spam is email that is received without asking for the purpose of promoting a business or advertising. Phone spam often occurs in text messages or calls. Spam is often annoying
C. What is a virus?
A virus is a program created to infect a system, it can damage or steal information, make copies of it and spread to other computers. These are called malware and there are too many that, if a computer does not have an antivirus, puts that information at risk. Viruses are classified depending on their actions and what they are programmed for
B. Antivirus
Having already installed an antivirus, these will protect you from:
Ransomware
Spyware
Trojans
Computer Worms
Viruses
Antivirus is the software or program that helps protect the computer equipment from viruses that arrive through any storage medium or other source and is used to detect and eliminate any type of virus on the computer and device even before there are infected the system. It is important to have antivirus software installed on the computer, only one, since, if you have two, one of them will mistakenly detect the other as malware and they will try to block each other and once they are locked the computer will be unprotected. The USB could also contract a virus and that is why the antivirus that we install is always up to date. Currently there are several antivirus programs that you can install, here are some of them:
Trend Micro Internet Security
Avira Antivirus Pro
Avast Premium Security
NortonLifeLock Norton 360
Kapersky Internet Security
A. Backup Copies
Another way to back everything up is in the cloud, which can store huge amounts of gigabytes of information. Information storage in the cloud is divided into:
Hybrid cloud storage. This type of storage combines the infrastructure of a local environment or a private cloud with the public cloud. This type of hybrid cloud moves information and applications from the public cloud to the private cloud and vice versa
Private cloud storage. It is the service offered in the data center or in the company's own intranet, using its own resources, which are not shared with other networks or users
Public storage in the cloud. Here, the user is subscribed to a certain plan with a provider, enters their information with an account and password. You can upload any type of information and share it
One way to avoid the loss / theft of information is to back it up to external memory such as USB. It is recommended to back up all the information constantly. There are different methods to store a backup of information, this is to optimize the storage and protect the content even more
Encryption. This method is used to protect information from potential security vulnerabilities. The encryption process becomes inconvenient since it consumes a lot of the CPU during
Reduplication. It specializes in understanding and is used specifically to eliminate duplicate data copies. To order storage
Redundancy. It allows you to generate backups from a computer to other external hardware or other device. It is very cloud-like
Compression. This method is used to reduce the weight of the saved files. It is safe and efficient
1.2.3 Storage on the Cloud
1.2.3.3 OneDrive
OneDrive is a cloud that allows you access wherever you are, you only need an internet connection. You can enter a document stored within it and edit or share it.
1.2.3.2 Basic Concepts
To talk about storage, you have to know some terms to know the magnitude of the cloud:
BYTE
it is used to measure the storage capacity of a device or the amount that is free in it. One byte represents one character, so if you have a text with a thousand characters, the file will contain 1000 Bytes
IP Address
An Internet Protocol (IP) or IP Address is a series of numbers that are used to identify and locate a computer equipment or any device that is connected to the Internet. Each IP of a device is unique and important for the transfer of information.
Why is my internet
so slow?
Some recommended tips so that your internet does not go slow is to use an ethernet cable, close the apps that are not used, that there are not so many people connected to the same network because this causes you oversaturation, avoid downloading heavy files.
Internet Speed
There are several applications today that help us measure the speed of the internet by measuring the ping, the rise and fall that we have. It is measured in megabytes per second that corresponds to the number of data that can be transmitted in a given time, here the concepts of the terms used to measure internet speed
Latency or Ping: It is the time it takes for the connection to communicate to the IP network and is measured in milliseconds.
Download: It is the time that the page where you are downloading something takes to download the installation data to the computer.
Upload: It is the time it takes your computer to send the data you send to the internet.
Bit
It is called the smallest unit of information that an electronic device can have. It comes from the abbreviation of 'Binary digit'. It only has one value, this can be 1 or 0. The concept is used to measure data transfer and internet speed transfer.
1.2.3.1 Introduction
Recently to keep our documents and data
we save it on the cloud, 'cause it´s more
practical
1.2.2 Virtual Machines
The concept of virtual machine is a program or software capable of loading another operating system into another, that is, it is an environment where one operating system is used to install another. It is not the same as hardware. With a virtual machine it is possible to have several operating systems installed. Some applications to create virtual machines are like 'VirtualBox', 'VMWare Workstation', 'Parallels Desktop', 'Hyper-V', 'Windows SandBox', 'Quemu', 'Xen', 'Boot Camp', 'Vertu', among other.
1.2.1 Introduction
Recently the storage capacity has grown and evolved enough so that today there are different providers that offer you storage services in the cloud. Information that you can have access to all day, anywhere, without space problems and without barriers. It is like an eternal memory, you can upload any type of content and information. One of the most important things that are stored in the cloud are the passwords that we use to enter websites. The cloud is safe but even so we as consumers must keep that type of very important information such as passwords.