por Y Alkandari 11 anos atrás
500
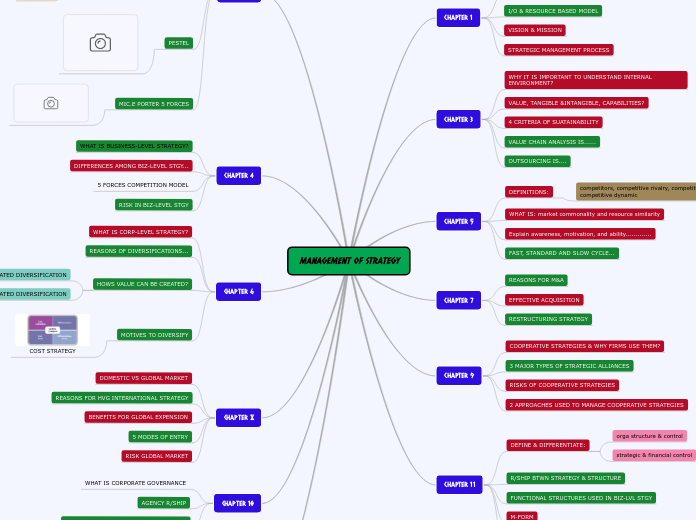
ToGaF9
The document outlines the various levels of architecture compliance, ranging from irrelevant to fully conformant, each describing the degree to which an implementation aligns with the architecture specification.